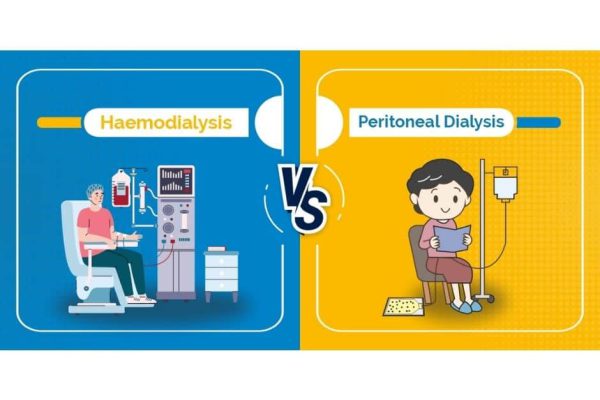
Hemodialysis vs Peritoneal Dialysis
Now a days kidney problems have become quite normal. Every now and then we used to hear about kidney failure of someone. When someone got damage his/her kidneys doctor advice him/her for the dialysis. There are two types of dialysis a patient can go for but due to lack of knowledge and understanding people get…